latest

February Pixel updates are here, with a fix for the 4a 5G's touchscreen issue and 'certain sensor detection'
We hope that's what we think it is
February 2021 updates for Google's Pixels from the 3 series to the 5 are landing today. On top of your regularly scheduled security patches, Pixel owners can also look forward to two other changes: A fix for the Pixel 4a 5G's touchscreen issue (which apparently extends to the Pixel 5 as well), and an undefined "fix for issue preventing certain sensor detection on startup," which could be tied to the long-standing Pixel device sensor issue.

Pixel 5 and 4a 5G get their first monthly updates with plenty of fixes in tow
Pixel 2 series left behind as planned
November updates are rolling out now for Google's Pixels, and that includes the brand-new Pixel 5 and 4a 5G. Functional patch notes mention a whole pile of fixes for both new phones, as well as older Pixels. That includes fixes for the screen waking at certain times when it shouldn't, inadvertently hidden system navigation during full-screen playback, issues with ringer audio for starred contacts in DND mode, and resolutions for a handful of Android Auto bugs. As expected, the Pixel 2 and 2 XL have no update this month.

Google announced Project Zero back in 2014 in a quest to make the internet more secure by researching software exploits and informing affected developers about them. The company soon adopted a 90-days public disclosure deadline in order to speed up the patching process. In 2020, this policy will change just a little bit. Previously, vulnerabilities were published as soon as developers fixed them, but now, Google will always wait the full 90 days until it reports to the public. That's meant to ensure that patches have rolled out to more users before potential bad actors know about the exploits, thus leaving fewer people vulnerable.

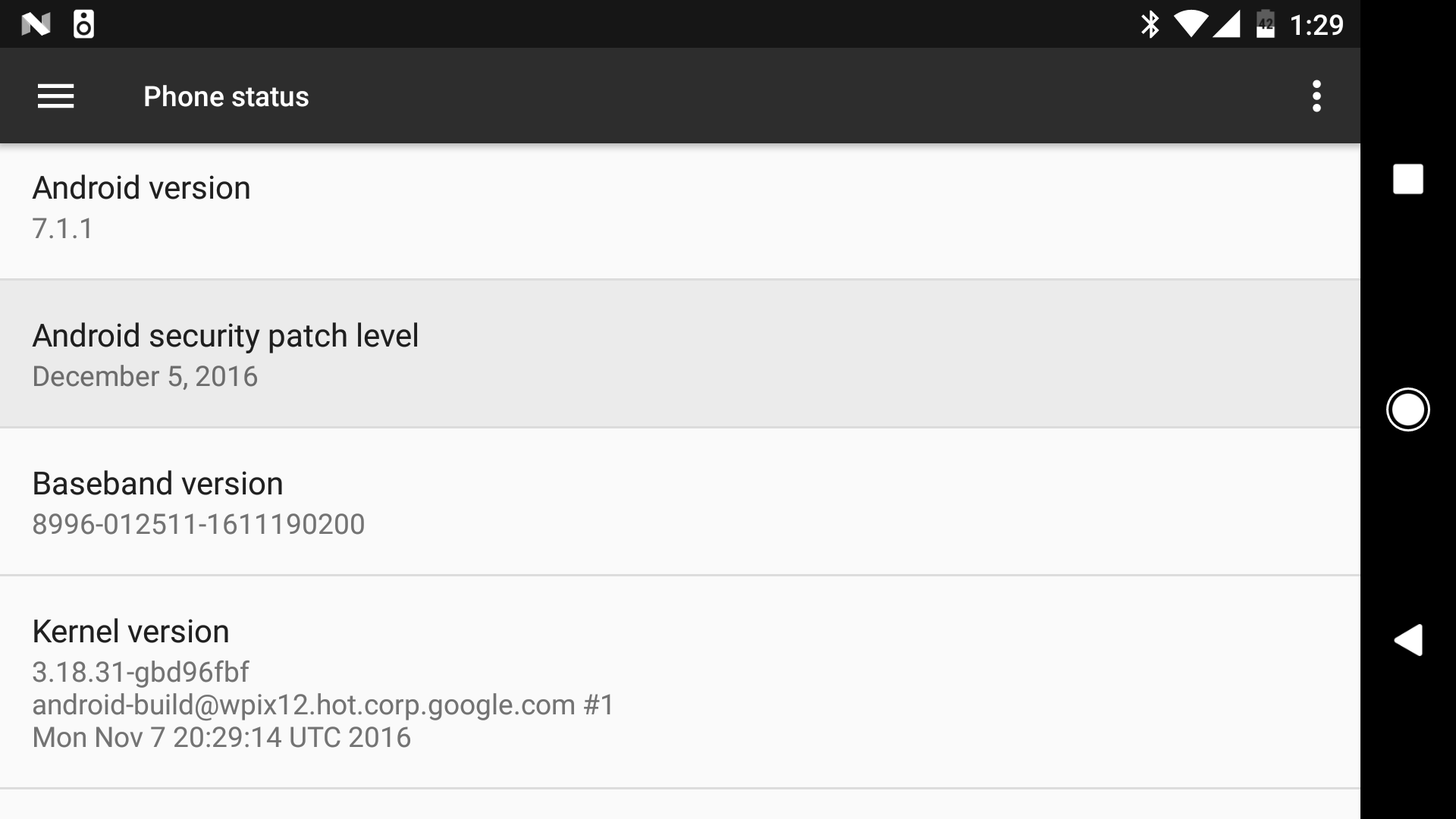
Another month is just starting, and that means it's time for the latest round of Pixel and Nexus patches to roll out. Google has posted both the system images and the OTA files, so you can get the latest version on your device without waiting for the update. You might actually want to go out of your way this time as there are some functional updates for Pixel devices.

It's time again for another update to Android, and it's rolling out to Google devices starting now. If you just can't wait for the OTA to reach you, there are some files you can download to skip the wait. It looks like most devices just have a single build this month, which will make things much easier.

Read update
Google is still working on getting the September security patches out the door, but it has posted a security bulletin detailing the changes. Several of the flaws noted in the bulletin are part of an enormous Bluetooth vulnerability discovered by Armis Labs, which bills itself as an IoT security firm. The "BlueBorne" attack exposes billions of Android devices to complete takeover by hackers, but it's not only Android. The same flaw exists in Windows, Linux, and some versions of iOS.

Google has been releasing monthly security patches like clockwork ever since it revamped the Android security model in the wake of Stage Fright. Samsung and LG are also trying to keep up with the monthly patches, but not always with the most success. LG's getting the jump on Google today, though. It has posted the January security bulletin a little early with information on Google and LG-specific patches.
There's an OTA update rolling out to Google devices today, but what sort of holes have been patched? Now you can find out with Google's latest security bulletin. Like the last few months, this one has multiple patch levels that you might see on devices going forward.

Google released a small update to Android Studio today to address a pair of potentially serious vulnerabilities recently identified in the IntelliJ platform. A blog post on the JetBrains website briefly describes the issues, both of which expose users to attack if they visit a specially crafted web page. The vulnerabilities exist in all versions of Android Studio before v2.1.1 and most or all IDEs based on the intelliJ platform. So far, there have been no reports of malicious attacks exploiting these security holes.

This week the latest batch of over-the-air security updates started rolling out to Nexus devices, most going under version LMY48M. Google also posted the goods online in the form of factory images. The company then went on to provide a list of the security fixes.

Back in October, Google announced a rewards program that would give financial incentives for "down-to-earth, proactive improvements" to security across third-party open-source projects that Google deems "vital to the health of the entire Internet."





