latest

PUBG: New State's latest update adds a new 4v4 deathmatch mode
Three new weapons have been added too
PUBG: New State's February patch is out today, bringing with it a bunch of new content and improvements, including a new deathmatch mode along with three new weapons, two new weapon customizations, a co-op revive/recruit function, a gift system for the in-game store, all while kicking off Survivor Pass Vol. 4. Of course, a litany of balance changes are here, including QoL improvements, bug fixes, gameplay updates, and performance optimization, rounding out this month's patch for PUBG: New State.

PUBG: New State's January patch lands with a new Extreme mode, kicking off the first season
Plus a new gun, fresh customizations, animation improvements, and much more
PUBG: New State is the new kid on the block. It's extremely similar to PUBG Mobile, but it offers a futuristic theme with improved graphics, amongst many other improvements. Well, even though you'd think Krafton would want to differentiate itself from Tencent's game, the latest patch for New State is rolling out today, a day after PUBG Mobile received its own update. Despite the confusing update cycles for both games, New State indeed offers a host of improvements and content with January's 0.9.23 patch. The most significant addition is the new Battle Royale: Extreme mode, which lasts 20 minutes, but fans can also expect a new weapon, new gun customizations, and new actions/animations. Plus, the latest Survival Pass (Vol.3) is now live.

Spider-Man swings his way to PUBG Mobile for a limited time starting today
Plus a new map and plenty more content for update 1.8
It's been two months since the last major update for PUBG Mobile, and so it's that time again to check out the latest content coming to the game. Update 1.8 begins its launch today, but it will continue to roll out over the next six days across the globe as new content is added. This odd and lengthy update period exists so that the game doesn't have to be taken offline to patch in the new content, so it would seem this will be the norm from now on. As for what's new, well, Spider-Man is in the game starting today, but only for a limited time; plus, there's a new Classic Mode map and a more secure matchmaking system, along with a litany of improvements. Let's dig in.

OnePlus 7, 7 Pro, 7T, and 7T Pro updates are here with May security patches
It also fixes some camera bugs and Google Fi issues
All four of the phones in the OnePlus 7 series are getting updated this weekend, patching the build of OxygenOS to 11.0.1.1. While this is mainly a series of bug fixes, the biggest change is upgrading the Android security patch to May 2021. The update is rolling out to the OnePlus 7, OnePlus 7 Pro, OnePlus 7T, and OnePlus 7T Pro now.

Google's May Android security update for Pixels is ready to go
We're not seeing a Widevine fix just yet
Pixel device owners, start your Wi-Fi radios. The monthly security update for Pixel phones has been posted by Google. The updates are available as both direct download of the firmware and OTA files, but it should be showing up on at least a few phones starting today.

OnePlus 7, 7 Pro, 7T, and 7T Pro get March security patch in OxygenOS 11.0.0.2
Other bug fixes are included in the quick update
Late last month OnePlus updated its most recent phones to OxygenOS 11, based on Android 11. As is common with major updates, a few bugs were found. According to its active user forum, OnePlus is now rolling out the 11.0.0.2 hotfix for the OnePlus 7, OnePlus 7 Pro, OnePlus 7T, and OnePlus 7T Pro, along with a security update.

Samsung recently revealed that it would give its phones an impressive four years of security updates. Paired with its high position in our regular Android update tracker, the company is rapidly becoming the Android update king. In light of the news, we're curious to know how up-to-date your phone might be. If you're willing to dig through the settings app for just a moment, let's compare: What Android security patch level is your phone running?
Twitter finally gets around to patching Android app security hole... 22 months later
An attempt to show it cares about security
Twitter has patched its app from a vulnerability within Android that could let a malicious app siphon users' private date — including their direct messages — while bypassing system permissions. Every Twitter for Android user was notified about the security hole which affects users on versions 8 Oreo and 9 Pie.

Minecraft 1.16.0 adds new Nether biomes, enemies, materials, music, and much more
Minecraft’s monumental Nether update is here
It's been a while since we've covered a new Minecraft patch, but it would appear the launch of the 1.16.0 Nether update is a big one. Four new Nether biomes have been introduced to the game, along with a new block material Netherite, not to mention a few new enemies. There's also new story content, plus you can expect to discover some fresh music as you explore the new areas in the Nether. As you can see, the Nether update brings many welcome changes, and you can jump in right now since Minecraft's latest update is already live on the Play Store.

Mozilla has patched a zero-day exploit in late revisions to Firefox 72 and version 68 of the Android web browser. In a security advisory, the company said that it was made aware of "targeted attacks in the wild abusing this flaw."

Android Q Beta 2 brought with it a lot of new features, though it's not surprising that some stuff is being broken given that it is a beta. Google today announced a patch for Q Beta 2, and factory and OTA images are available for installation right now. OTAs will roll out within the next 24 hours.

The Fortnite mobile beta is still limited to Samsung users and those that have received beta invitations. Since development on the title is a constant, it's no surprise to see a new patch rolling out today. The big news is that this patch brings with it voice chat for Android. You can also expect to find a new capture-the-flag mode called Getaway that will only be available for a limited time.

One week ago, details about widespread vulnerabilities in modern processors became public. One variant, named 'Meltdown,' affected every modern Intel chip. Two other variants, collectively known as 'Spectre,' are known to affect chips from Intel, AMD, and ARM (at the very least). Most Google products are already protected against these threats, but now the company has made it easier to tell which Chromebooks are patched.

Vulnerabilities. There's a new flavor of the week every few days and in this highly connected world, it's tough to keep up, whether it's for users who don't know which of their devices are vulnerable and have/haven't been patched or for companies who are scrambling to fix one bug only to see the next one around the corner.

Root users should be universally familiar with Magisk, and yesterday both it and the associated Magisk Manager were updated to v14 and v5.3.0, respectively. There are a ton of changes, but the headlining features from these updates are improvements in Samsung device compatibility, a new beta channel for updates, and the ability to patch boot images without root. That last one is a biggie, as it'll let you install Magisk both without a custom recovery and without already being rooted.

OnePlus is something of a darling among Android power users, shipping phones that can be bootloader unlocked without any special permissions or codes. But security researcher Roee Hay found that the OnePlus 3 (and the revised OnePlus 3T) are rather more open than was probably intended. With two native fastboot commands, Hay found he could install unverified boot images and disable the verified boot feature, all without actually unlocking the bootloader with the familiar user-accessible command. Which is, well, bad: it basically means anyone can run malicious code on the phone without resetting the user's data.
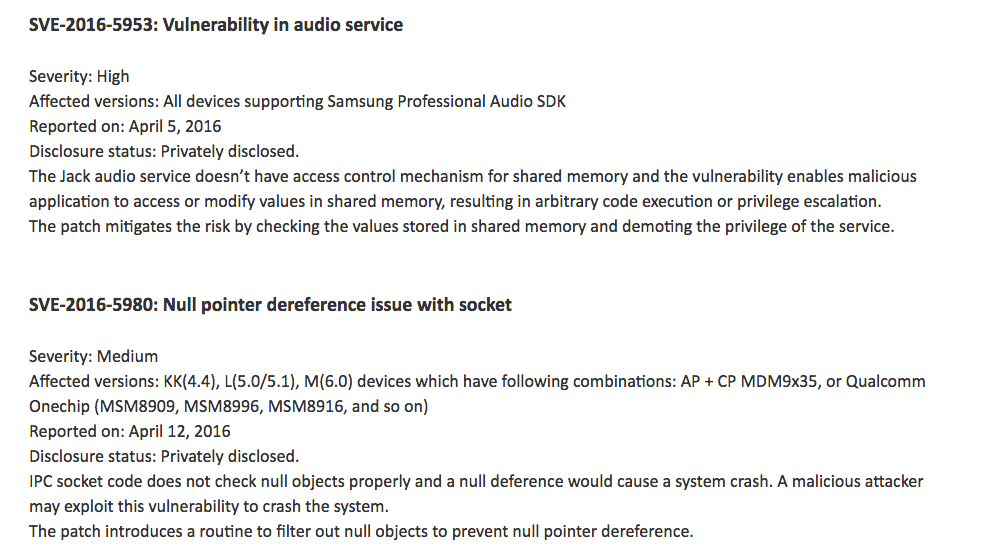
Samsung has been diligent about releasing its security patch bulletin along with Google at the beginning of every month, but this month, it took the lead and published the details before even Google got around to doing so.

Google and the various major Android device vendors and carriers are scrambling to patch the recently-discovered Stagefright exploit, a weakness in Android's multimedia processing that can allow remote access via a simple MMS message. Google has already begun patching Nexus devices, and Samsung is working its way through its extensive product range starting with flagships. Yesterday Motorola released its plans to update its phones.

So you might have heard about the Stagefright vulnerability that was published yesterday. While there's no evidence of a widely-used hack, the potential for malicious MMS attacks via Android's built-in media handling system (which could theoretically affect the majority of Android devices currently in operation) is certainly cause for concern. As reported on our original post, Google has known about the vulnerability since April and has been working on patches to fix the problem.

While the experience isn't felt across the board, many OnePlus One owners have been plagued by touchscreen issues since making the decision to never settle. As a result, the company has pushed out update after update aimed at alleviating an issue that seems to have a tendency to resurface.







