latest

The top 11 WhatsApp scams and how to avoid them
No, there is no free WhatsApp Gold tier with extra benefits
WhatsApp's popularity in the instant messaging space makes it a favorite platform for fraudsters to scam users. WhatsApp cybercrime has increased, costing victims thousands of dollars. Fraudsters use several tricks to trap you and extract your personal and financial details. Keep the points below in mind and look for clues to spot a scam on iPhone and Android so that you don't become a victim of a WhatsApp scam and lose your hard-earned money.

Snapchat is a feature-packed messaging app with a paid plan that gives power users access to experimental, pre-release, and exclusive features. Among the Snapchat Plus features, the Friend Solar System is an interesting add-on that allows you to rank and visualize your closest friends. Snapchat is available on the desktop, but the ability to check your solar system is available only on iOS and Android phones. Keep reading to learn about Snapchat planets, their order, and their meaning. You'll also find a trick to check your ranking in your friend's solar system.

Warcraft Arclight Rumble guide: Navigate Blizzard's mobile strategy game
How to collect and command an army of Warcraft Minis
One of Blizzard's most prominent franchises was always World of Warcraft (WoW), and if you didn't happen to own a PC, you might've skipped it entirely. But Blizzard's latest mobile game will finally bring the magic of the WoW franchise to another platform. So, to commemorate the legacy that WoW has left behind, Blizzard has constructed a mobile action strategy game, Warcraft Arclight Rumble.

How you can install and play Fortnite on Android
Fortnite may have been kicked from the Play Store, but you can still play the game on Android
Epic Games did a big no-no in 2020 by releasing a Fortnite update that circumvented Google's in-app payments. As a result, Google removed Fortnite's listing from the Play Store. The whole fiasco left players with limited options for regaining access to the official Fortnite app.

Pokémon Go beginner's guide: How to get started in 2024
Start your Pokémon GO journey with a handbook that won’t go out of print
Niantic's Pokémon Go is one of the best Android apps to bring outdoors. Since the app's release in 2016, Pokémon Go has sent Pokémon trainers into the wild (also known as our backywards). Thanks to its steady monthly earnings, the game has stayed afloat with new updates and features. As new generations of Pokémon get added, Pokémon Go sees a healthy amount of installs to attract new prospective players. Even today, you won't find another AR-based game like Pokémon Go.

What is Roblox? Navigate the popular game creation platform with ease
Millions of daily active users still play Roblox, an app that's over a decade old
As we know it today, Roblox is a social platform-turned-metaverse where prideful gamers (of all ages) develop and share their creations while indulging in community-driven games. Roblox has left a legacy that's attracted a supportive community and following, which is a large part of why the aging platform remains intact today. Roblox is more than just a massive sandbox/simulation game; it reels in a large, growing community and brings indispensable resources to get gaming creations out to the world without needing a top-end Android phone.

Summoners War Chronicles guide: How to get started defending the Kingdom of Rahil
Lean into the power of comradery with this high-profile gacha game
Com2su Studio brings another pet-companion collector, Summoners War, to mobile and PC. Some may already be familiar with the name, as Summoners War made the rounds on mobile devices a decade ago and is still alive and kicking. Com2su Studio aims to revitalize the Summoners War series by introducing a new game to modern-day (compatible) devices. So, if you've never dipped your feet into the franchise before, Summoners War: Chronicles provides more than a solid enough entry point.

Limbus Company guide: Manage the seven deadly sins
Learn how to lead your unruly group of sinners across The City
Limbus Company is the latest occultic RPG by Project Moon. It serves as a sequel (taking place in the same universe) to classic hits Lobotomy Corporation and Library of Ruina. Both of those games have a strong showing on Steam, scoring 9/10. Based on Project Moon's impressive resume of games, these developers know how to deliver a gruesomely dark story with a high degree of mechanical complexity. So Limbus Company becomes a welcomed title as the first Project Moon to arrive on Android, which no doubt slinks itself to be a banger of a game on Android.

Best Vampire Survivors secrets and unlocks
Looking for an edge to last longer? Try unlocking a few of the game's secrets to reign supreme
There are lots of reasons for the continued popularity of Vampire Survivors, not least of which is its low price point (free on Android!). But low prices will only get players through the door. What keeps them coming back to one of Android's best games again and again is the sheer abundance of content. Whether that's unlockable items, DLC, or massive updates that keep the game fresh, there's always something else to discover. But it can be daunting trying to make sense of all the content if you're a new player or if you're coming back after a break. And while you're delving into all the secrets Vampire Survivors has to offer, you should take a peek at these not-so-secret top-tier gaming phones.

Final Fantasy VII: Ever Crisis guide — Explore Midgar like a pro
Coping with Shinra's greedy capitalism is no easy feat
Final Fantasy VII: Ever Crisis was one of our most anticipated Android games in 2023. The Final Fantasy franchise has a history of delivering some top-notch stories that can be loaded onto any favorite Android gaming phone. Now, with Ever Crisis available as a free-to-play mobile and PC title, you can finally play through the entire Final Fantasy VII compilation.

Pocket City 2 guide: The best strategies to grow your town
Everything you need to know to not get lost in your own city
If you're a fan of city-building games in the same vein as SimCity and you've been sleeping on Pocket City 2, you're missing out on one of the best simulation games Android has to offer. Pocket City 2 stays true to its isometric city-building roots while reinventing itself by allowing you to explore your city on foot, street racing in a car, or from above in a hang glider. If you've played the original Pocket City (or any similar game for that matter) you shouldn't have any problem jumping in on your new gaming phone, but if this is your first time dabbling in a city sim, we've got this handy guide to get you started.

What is Preferred Care for Pixel devices?
Preferred Care for your Pixel hardware saves you from an eye-popping bill during an unfortunate incident
While you have ample accessories to protect your Pixel phone, watch, tablet, or foldable, an unfortunate incident can break down your hardware in no time. Hardware defects, software glitches, or unexpected water damage can ruin your Pixel experience, especially when it's your primary device to get through a busy day. Your Google Pixel has a one-year manufacturer's warranty, and you can purchase Preferred Care to extend the warranty and enjoy hassle-free repairs.

Aether Gazer guide: Tips and tricks to re-roll like a pro
Is Aether Gazer a Honkai Impact 3rd and Punishing: Gray Raven knockoff?
Aether Gazer is an action RPG published by Yostar, the same publisher responsible for other well-renowned gacha titles: Azur Lane and Arknights. Most compare Aether Gazer's action RPG gameplay to Honkai Impact 3rd and Punishing: Gray Raven (PGR), which are also considered some of the best gacha games on Android.

How to stop your games and apps from crashing on Android
What the heck is an unhandled exception, and what can be done about it?
There's nothing more maddening than being immersed in your favorite Android game only to have it unceremoniously crash. In an instant, you're robbed of potentially hours of progress in your RPG, forcing you to laboriously grind the same levels and beat the same bosses again. Other than throwing your phone out of a window in disgust, how can you keep this from happening to you, other than upgrading to an awesome gaming phone, of course?
.png)
Wordle guide — From novice to expert in an afternoon
Don’t miss out on the latest word game trend sweeping the web
Since the most popular Word game flooded social media posts in 2022, plenty of Wordle posts remain in the spotlight today. Sharing and discussing daily puzzle results online has become a routine for millions of players. Once you've got a hot streak going, it becomes tough to call it quits.
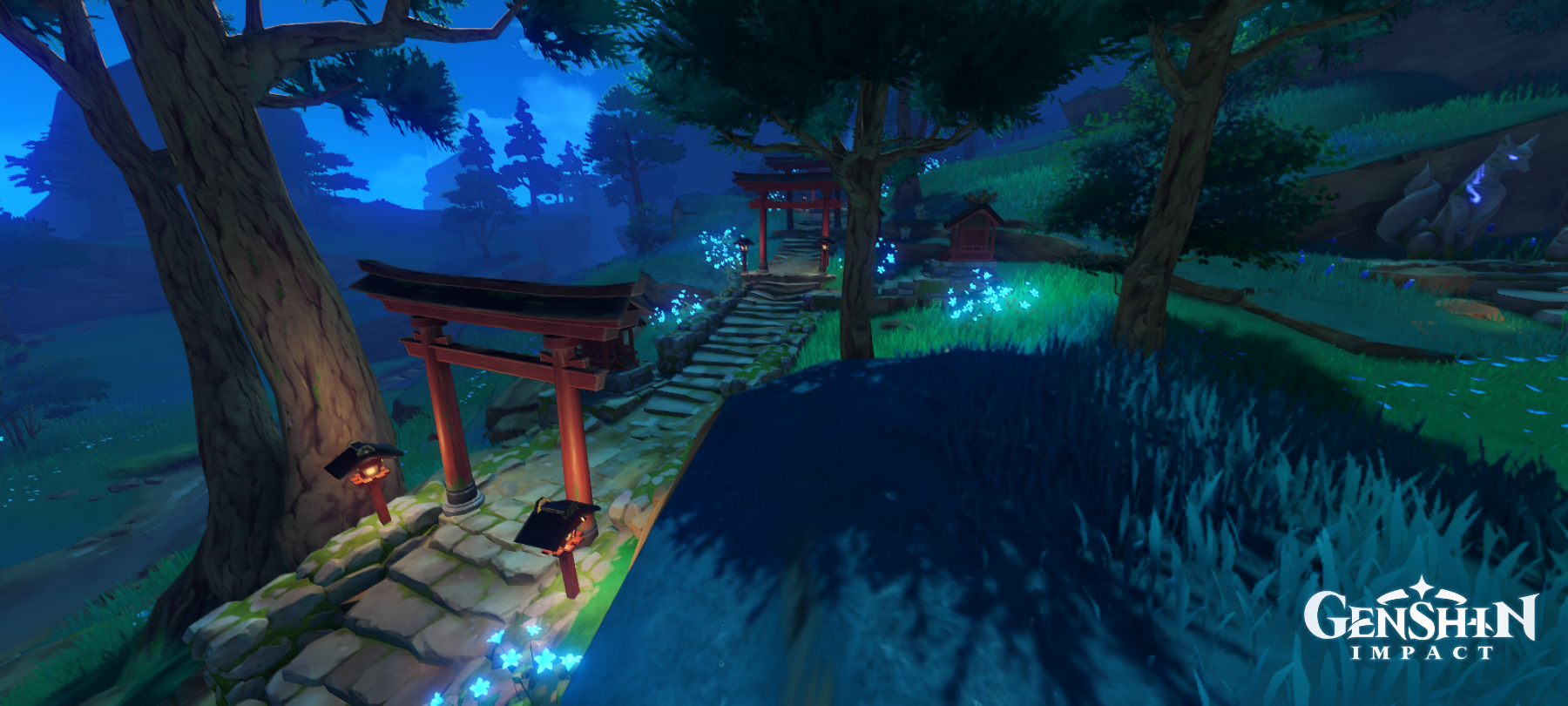
Genshin Impact guide: How to reach the city of Inazuma
This isolated archipelago isn't easy to reach, so here's what to do
Even after an astronomical successful launch period, HoYoverse's Genshin Impact still holds a seat as one of the best Android games on our mobile devices. Genshin Impact is a beautifully polished free-to-play open-world adventure RPG that successfully sets the standards for top gachas to play on your Android gaming phone. And despite the competitive live service market, HoYoverse continues to churn out some substantial updates (patches) every six weeks. It's also rumored that HoYoverse has cooked up a ten-year roadmap for this title.

Torchlight: Infinite guide — Getting started in the era of Ember Technology
Jumpstart your class in latest game in the Torchlight ARPG series
The Torchlight's history has been a rocky one. The series went through a streak of bad luck thanks to scrapped projects and canceled sequels. Xindong Network and consulting producer David Brevik (former Diablo series creator) have brought Torchlight: Infinite to PC and mobile as one of Android's best games.
Yu-Gi-Oh! Master Duel guide: Tips and tricks for beginners
Everything you need to know to play like a pro
In early 2022, Konami finally brought over a true digital Yu-Gi-Oh! trading card game (TCG), Yu-Gi-Oh! Master Duel to multiple platforms, including Android and iOS. It's not the first time, Yu-Gi-Oh! has arrived on mobile platforms. But none have shared the traditional (official TCG) ruleset. But a game staying true to one of the most popular TCGs in the world is enough reason to consider Yu-Gi-Oh! Master Duel as one of the best Android games to come out recently.

How to request a refund on Steam to return your game
Returning a game on Steam is as easy as following a few simple steps
After loading up on Steam gift cards and redeeming Steam keys, you might be disappointed with some new additions sitting in your Steam library. Unfortunately, we all live to regret some impulsive purchases, and those games become an eye sore when we spot a flash sale (with the same games) not too long after. No matter the reason, we should always consider returning those Steam games. But going through hoops to put in a request to Valve might seem like a daunting process. But to streamline the Steam games refund process, we created a handy guide that teaches users how to return games on Steam with the essential guidelines that follow it — this way, you can get back to managing your Steam library through your favorite Android tablet or phone.

How to create a Gantt chart in Google Sheets
What's a Gantt chart? How do you create one? Find out in this guide
Various tools and utility apps have improved work on contemporary Android tablets. With the right combination of tools, you can do most of your work without relying on a traditional laptop or PC. One of these tools is the Gantt chart. In a nutshell, it tracks and displays your progress across multiple projects.




