latest

Google will start scanning for Android malware in real time
Having to worry less about what's on your phone is a win in our book
Android is about as open as operating systems get these days. Compared to iOS, which allows very little wiggle room for non-Apple authorized customization, Android users can do almost anything to their phone — for better or worse — with a little bit of tinkering. One of the ways people can utilize the openness of their smartphone is by sideloading apps outside the Google Play Store, which can obviously be a bit dangerous regardless of whether you’re as careful as they come with technology or not. Malware can come in all shapes and sizes, so Google has taken the steps to finally roll out an enhanced version of Google Play Protect, which we mentioned was being worked on last month.

Google beefs up security features to keep you safe online
Safe browsing, dark web scans for your Gmail address, and more
The world is a dangerous place, and your personal information is constantly being targeted by criminals. While you have no control over large corporations' security practices, you can take steps to protect your own data online. To that end, Google has introduced a number of measures to make you feel safer while browsing the web, including expanded data controls, dark web scan for Gmail, new ways to better identify scam websites, and more.

Android 12 adds an option to deactivate 2G for security reasons, but your phone may not allow it
2G has become redundant in some regions and only serves as a means of attack
Android 12 officially launched in October of last year and several OEMs have pushed the new OS to their eligible smartphones and tablets since then. While features like Material You and improved widgets have garnered mainstream attention, more recent additions have somewhat flown under the radar. One such inclusion is a 2G kill switch that has recently come to light.

Google has gotten a bit stricter with requiring OEMs to add Android's security updates over the years, but that doesn't mean companies are actually on board. LG's Software Update Center may be running at full power, but everything from last-minute bugs to carrier certification can hold up Android updates. It's almost July, but LG's new dual-screen capable device is only now receiving the May security patch.

Researchers finally discover how Android malware that could survive factory resets works
A Kaspersky researcher uncovered the secrets behind xHelper malware's incredible persistence
Earlier this year, a story made the rounds about a new kind of malware afflicting Android handsets. But it was this malware's pernicious nature that really made headlines, as it could even survive complete factory resets on afflicted phones. This insidious malware was named xHelper. At the time, we didn't know how it managed this impressive (but scary) achievement, but security researchers at Kaspersky have since dug into its inner workings, revealing an incredibly sophisticated system that installs itself to an Android phone's system partition, and even changes how the system works to prevent it from being "easily" removed.

Samsung may have removed the iris scanner from its recent flagship devices like the Galaxy S10 and Note10, but it hasn't forgotten about it on earlier hardware. According to some Galaxy S9 and Note9 users in the Android 10 One UI 2.0 beta program, the company has updated the iris scanner in those phones to be compatible with Google's new Biometric API, a one-stop-shop for in-app user authentication.

A new security vulnerability has been discovered inside the Android camera app that potentially affects hundreds of millions of phones across the world. Discovered by a team of security researchers at Checkmarx, the exploit allows a malicious app with access to a phone's storage system to bypass Google's permission safety net and completely spy on users.

Although 5G is often touted for being newer, faster, and more secure than 4G, a team of security researchers from the University of Iowa and Purdue University has flipped the last bit of that marketing message on its head by discovering almost a dozen new 5G vulnerabilities. As a result of these breaches, they were able to carry out some nasty attacks like location tracking, broadcasting of false emergency alerts, and severing the 5G connection of a phone entirely from the network.

A group of security researchers has discovered an exploit that lets Bluetooth and USB accessories wreak all sorts of havoc on multiple Android smartphones. In both cases, the door of entry was the cellphone modem, or baseband, which is found inside all smartphones.

Read update
Smartphone users already have several great options when it comes to password managers on Android, letting them log in to supported apps at the press of a button. Now they're being joined by ZenKey, a new service developed in collaboration with the four major US cell carriers that's looking to do away with individual passwords while claiming some robust security features of its own.

Promptly on time, Google has released October's OTA files and factory images for the Pixels, as well as its general Android security bulletin for the month. At the same time, Verizon is pushing out the set of patches to Pixel users now. It's the second update to Android 9 Pie, and this time around there are no Pixel security patches — just a few functional patches including, most notably, what might finally be a fix for the 2016 Pixel fast charging bug.

The Wi-Fi Alliance has announced additional measures to secure wireless devices, following revelations last year about an oversight in the WPA2 specification which left devices vulnerable.
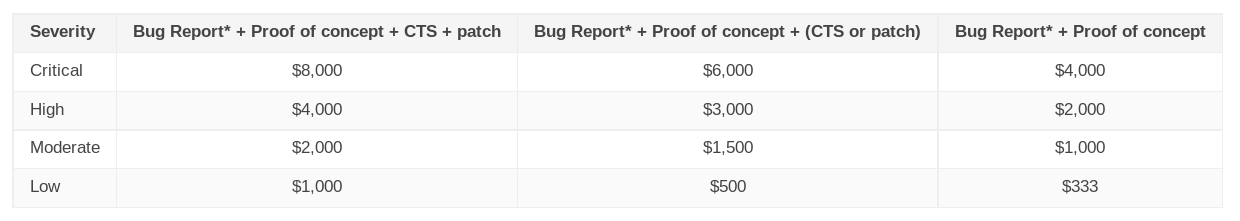
A year ago today Google announced Android Security Rewards, an expansion of its Vulnerability Rewards Program. Find a vulnerability, tell Google about it, help them fix the issue, and take home money. That's the concept, and it's a common one in the tech industry.