Read update
- More details
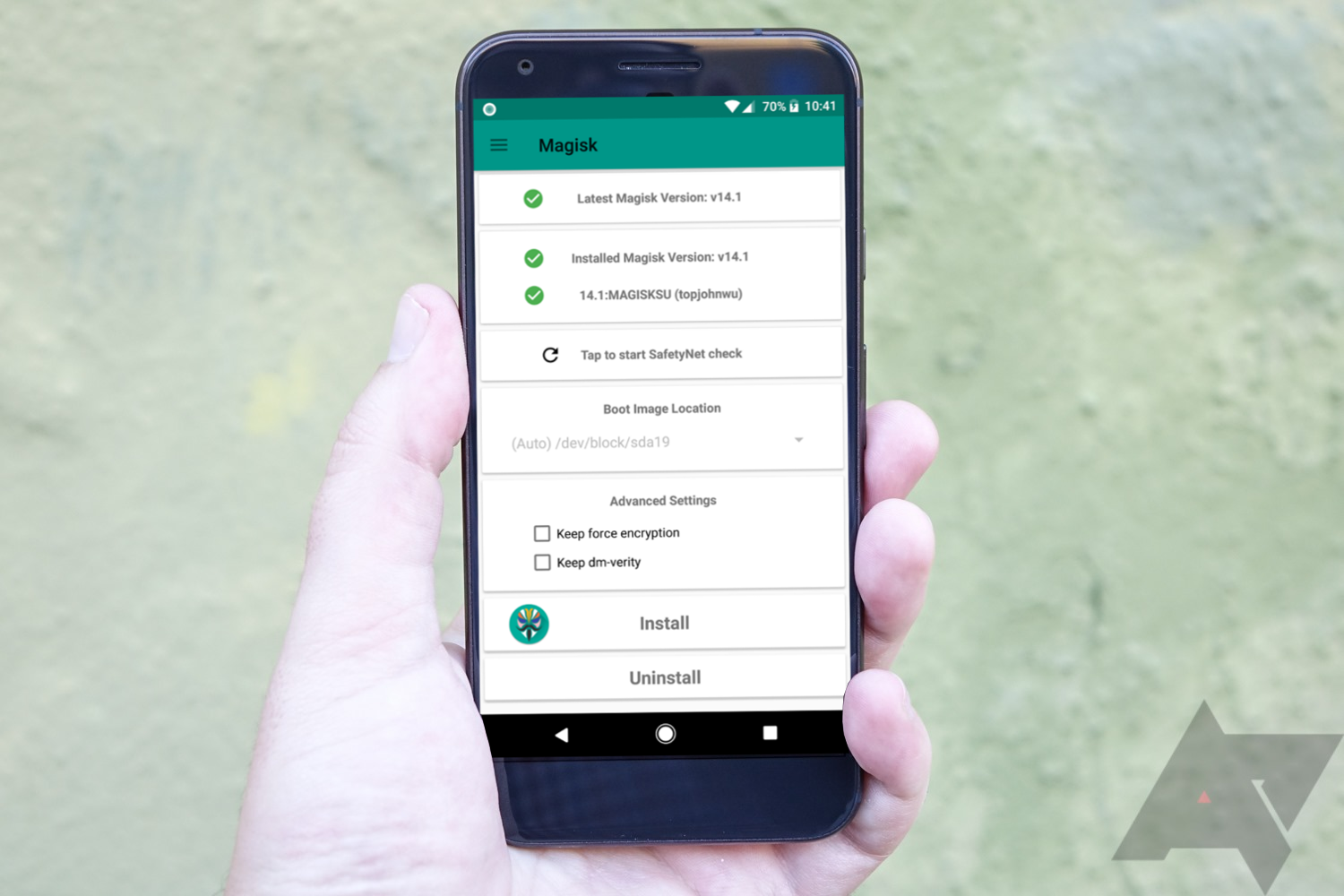
Magisk and Google have been playing a game of cat and mouse for years: Google's SafetyNet technology is supposed to be triggered when it notices a rooted device, but MagiskHide does its best to keep banking apps, Pokémon Go, and other root-despising applications going, no matter what you do with your phone. However, the latest update to SafetyNet, apparently rolling out via the Play Services, seems to put an end to the game permanently. Magisk developer John Wu isn't convinced he'll find a solution that would keep his tool intact once Google fully implements the change.
John Wu describes on Twitter that the recent update properly uses SafetyNet's key attestation API that remotely verifies a device's security status. It looks like Google hasn't utilized this check to its full potential previously. In order to hack the API, developers would either need to find a vulnerability in the Trusted Execution Environment (TEE) in Android, a mini OS responsible for security-relevant tasks, or a hardware vulnerability. Both solutions come with difficulties: TEE could be fixed via a software update, and Google and other manufacturers pay out thousands of dollars to anyone who finds breaches in their hardware, meaning that the companies are pretty convinced they're hard to hack.
For the moment, John Wu and his team should be able to work around the issue. The key attestation is not fully enforced yet — even when the check fails, SafetyNet still isn't triggered. That's probably due to a few OEMs like OnePlus that haven't implemented the key checking feature correctly on their part. MagiskHide could thus force a key attestation failure to pass SafetyNet. However, John Wu notes that any solution he can currently think of would fail once Google fully deploys the change to SafetyNet that processes the attestation on a Google server, outside of Magisk's reach.
Even though Wu's Twitter thread is considerably pessimistic, we shouldn't give up MagiskHide just yet. The developer has overcome seemingly impossible odds before, and it's certainly thinkable that he can do it again. Even if John Wu doesn't find a solution himself, another intrepid developer might come along and discover one — so far, it has always worked out. Let's hope for the best.
UPDATE: 2020/03/12 12:53am PDT BY MANUEL VONAU
More details
John Wu has shared more details on the change on Twitter. He confirms that MagiskHide will continue to conceal root, but it might soon not hide the fact that your bootloader is unlocked anymore, since that's what SafetyNet checks for. Other than that, he expands on why he doesn't see a way around Google's new implementation: The problem is that the new key attestation workflow is hardware-based, and the code is sent to Google's server, so as long as there isn't any vulnerability in TEE, it's unlikely that MagiskHide will be able to alter the key or intercept the transmission.
UPDATE: 2020/04/03 3:29am PDT BY MANUEL VONAU
No progress in sight
A few weeks after the original Twitter thread, it still looks like John Wu can't find a quick or simple solution to the problem. He does say that it's not impossible to hijack the new SafetyNet implementation, but it doesn't seem like he's able to break into TEE to do that himself. We can only hope that some solution can be found for people relying on both root and an intact SafetyNet.
UPDATE: 2020/06/29 8:18am PDT BY RYNE HAGER
Spotted in the wild
The change has been spotted in the wild, and the days of carefree root/ROMing are almost over.
Source: @topjohnwu