A new piece of Android malware has been discovered by security researchers at Kaspersky Labs. That by itself wouldn't be big news, but this Trojan does things no other malicious app has done. It exploits multiple vulnerabilities, blocks uninstall attempts, attempts to gain root access, and can execute a host of remote commands. Backdoor.AndroidOS.Obad.a, as it has been dubbed, is the most sophisticated piece of Android malware ever seen.
There are two previously unknown Android vulnerabilities exploited by Obad. The malware installer contains a modified AndroidManifest.xml file, which is a part of every Android apps. The first big vulnerability is in the processing of this file by the system – it shouldn't be processed at all, but the app installs just fine. Once Obad is on a device it uses a second Android exploit to gain extended Administrator access. The Android Administrator feature allows apps to read notifications and perform other advanced operations (a lot of security apps use it). When this command is executed, Obad can not be unsinstalled and it doesn't even show up in the list of Administrator-approved apps.
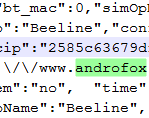
When it is in place, Obad starts probing the system and checking for internet and root access. It slurps up data and reaches out to its command and control servers. Here is the full list of command functions described by Kaspersky:
- Send text message. Parameters contain number and text. Replies are deleted.
- PING.
- Receive account balance via USSD.
- Act as proxy (send specified data to specified address, and communicate the response).
- Connect to specified address (clicker).
- Download a file from the server and install it.
- Send a list of applications installed on the smartphone to the server.
- Send information about an installed application specified by the C&C server.
- Send the user’s contact data to the server.
- Remote Shell. Executes commands in the console, as specified by the cybercriminal.
- Send a file to all detected Bluetooth devices.
When it arrives on a device most of the package is encrypted, and some of the most important components are not decrypted until it gains internet access. This makes analysis and detection much more difficult. The Trojan doesn't even have an interface – it works entirely in background mode. The level of sophistication and new exploits in this one piece of malware looks more like a Windows virus than other Android Trojans. Backdoor.AndroidOS.Obad.a is still very limited in scope, but it is floating around alternative app stores and fishy websites.