latest

Sunshine 3.1 Adds S-OFF Support For HTC One M9 And Automatic SIM Unlock For Most Of HTC's GSM Phones
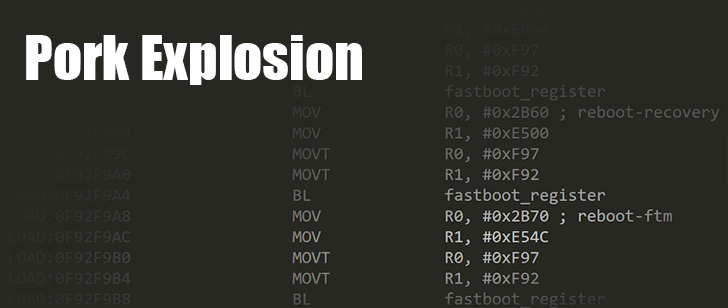
New smartphones are rolling off the line pretty regularly, and that means the tools we use to work with them have to update, too. Last month, Sunshine v3.0 emerged with support for an extensive collection of HTC and Motorola handsets, and now an update to v3.1 is about to build on that list. With the latest release, Justin Case and Beaups have added support for almost every variant of the HTC One M9, except Verizon's. Expanded compatibility isn't the only new treat for users, Sunshine has also added the capability to automatically SIM unlock most of the GSM-based phones manufactured by HTC.

Read update
If you're going to do any serious modding on your Android smartphone, your first step is going to be unlocking the bootloader. This is a simple procedure on Nexus devices and a few other handsets, but many of the top OEMs have added security measures to prevent regular users from mucking about with their stock software. For these devices, there's a tool called Sunshine by recognized developers Justin Case (jcase), beaups, and friends. Version 3.0 just came out, and it can unlock the bootloader and acquire S-Off with almost every modern Motorola and HTC smartphone on the market.
Back in March, Justin Case released a root tool called WeakSauce for HTC's flagship lineup on Verizon. Unfortunately, a steady procession of updates to each handset has patched the original exploit, leaving many without root. Now there's a new version of WeakSauce, and it can root just about every HTC phone on Verizon running Android 4.4.4 and below.

Much to the chagrin of cell carriers and hardware manufacturers, there are still many in the Android community that choose to delve into the world of hacking and modding their phones. Owners of the Verizon Moto G are certainly in this crowd, and they've been eagerly awaiting a reliable method for unlocking their bootloaders. It turns out that their wait ends today. Sunshine, a tool built by Justin Case, Beaups, and others to unlock HTC and Motorola phones, just gained support for the Moto G on Verizon.

Love it or hate it, the LG G3 is one of the top flagship devices of 2014. With a set of specs that will make even the most jaded Nexus warrior a bit jealous, it's no wonder that the handset has gained a few fans. Unfortunately, LG's software customizations still leave a lot to be desired, and many users have turned to rooting their phone to take back some level of control over the experience. A handful of root tools have come out with support for most of the US and international variants, but none of them worked across the board, and the Sprint model hadn't been cracked at all. That is, until Stump Root. Thanks to a new tool by Justin Case, IOMonster (thecubed), autoprime, and PlayfulGod, you're one button press away from rooting any US variant of the G3.

Ask anybody that spends time in the security circles and they'll tell you that every large software project is bound to have a few long-standing vulnerabilities in the code. Fortunately, there are usually a few people who are paid to close up those holes so you, the customer, don't find yourself the victim of nefarious evildoers someday. Like so many before it, the latest update to Android came with a boatload of changes, at least one of which fixes a potentially dangerous vulnerability that can be used for numerous attacks, including a way to acquire root.
You've taken the plunge and thrown down some cold hard cash on a brand new HTC One M8, but you're feeling stifled because Verizon doesn't want to allow the bootloader to be unlocked? You might want to check out WeakSauce, a handy new root exploit by XDA recognized developers Justin Case (jcase) and beaups. It's a simple tool that can set up root on both the HTC One M8 and last year's model, the HTC One (codenamed M7).

Any decent bank heist movie always has one common hurdle for the would-be thieves: a regularly changing access code to the vault, and only one person knows what it is. Haven't you ever wanted that kind of security on your phone? This is now possible with TimePIN, a light-weight app that changes the access code to your lockscreen every minute.

Some Moto X owners weren't particularly happy to learn that a recent OTA with improvements to the camera also had the undesirable consequence of breaking root acquired through PwnMyMoto. Fortunately, the creator of PwnMyMoto, Justin Case, is back with an updated root method that works on the latest Moto X update and should be compatible with all recent Motorola firmwares.

That didn't take long. Just 2 days after Justin Case released a root method for the Moto X, Droid Ultra, Droid Mini, and Droid Maxx, he's already back with a hack that bypasses write protection. By disabling the write protection afforded by the bootloader, it becomes possible to flash 3rd-party ROMs, themes, and other mods. In other words, the flood gates are open for the modding community.

When buying used phones off of eBay, Craigslist, or the like, a primary concern of anyone purchasing CDMA devices (Verizon, Sprint, Boost Mobile, Virgin Mobile, etc.) is the status of the phone's ESN (electronic serial number). If a device's ESN is registered as "banned" on its carrier because it has been listed as stolen or is attached to an unpaid account, then that phone cannot be activated on said carrier. Thus, the phone is either useless or has to be activated on a pre-paid carrier, which is generally not all that desirable and drastically decreases a device's worth.

Justin Case has done it again, bringing root access back to users of Amazon's Kindle Fire who accepted the recent firmware update to version 6.2.2. BurritoRoot 2 is an easy-to-use exploit that only requires adb (Android debug bridge) and a few moments of your time. Users looking to root their device after Amazon's latest firmware update can grab BurritoRoot 2 using the download mirrors below.