latest

You probably know Chainfire from his work on SuperSU, which he stepped away from last year. Chainfire's latest project isn't quite as complex, but it is pretty timely. The Galaxy S10 launch has spawned a community dedicated to making wallpapers that celebrate the hole punch display, and Chainfire's Hidey Hole app puts all those wallpapers in one place.
Chainfire is best known for creating SuperSU, one of the most popular superuser managers on Android, but he has also developed countless other applications. Some examples include FlashFire, Sideload Launcher for Android TV, stickMount, and CF.lumen. He transferred SuperSU to a new development team back in 2015, and his involvement in the app ended last year.
It has been just over two years since Chainfire announced the sale of root tool SuperSU to a newly formed company called CCMT. Despite some initial fears, this transfer of ownership hasn't negatively impacted users, and SuperSU is still chugging along. However, Chainfire's two-year contract with CCMT is running out, so it's time for him to move on. To what? Lots of things, probably.
SuperSU is an app that any rooted user will know, even if you don't use it. I have fond memories of it from my days rooting and ROMing every device I could get my hands on, and it would appear that I'm not the only person who feels this way — SuperSU just hit the impressive 100 million downloads mark.
Users looking to hide their root status from being detected by things like SafetyNet now have one more option available, aside from Magisk. Chainfire, the original developer of the closed-source root solution SuperSU, has released v1.0 of suhide. This latest incarnation is "completely different from the old version," but should work about the same for the end-user.
In the wake of recent problems, a partial fix has been pushed for SuperSU. Root loss on older (pre-4.4/Kit Kat) phones should no longer be an issue. Unfortunately, this latest update doesn't fix the bootlooping some Sony Xperia phones are experiencing. If you're using SuperSU on one, you should continue to stick with 2.79 for now.

The Pixel smartphones' new partition system and boot images have been a hot mess for developers and tinkerers who like to push their devices beyond the specs written on the shipping box. But even though this has slowed down the release of custom recoveries and other mods, it hasn't completely stopped our beloved enterprising developers who probably thought of the whole situation as a nice challenge instead of an unsurmountable obstacle.

The Google Pixel phones' development has had a big week; just a few days ago, the Verizon and EE variants had their bootloaders unlocked. Now, Chainfire, the famed developer of SuperSU and FlashFire, has debuted a systemless root method for the Pixels.
Hiding your root status from apps that refuse to work when you are rooted—like Android Pay—is a cat and mouse game that enthusiasts have been losing lately. Chainfire, the developer who has become the main source of advances in rooting, announced today a new way to work around Android apps' ability to detect the root status of a device. The app, called suhide, works but comes with a number of caveats.

Android developer extraordinaire Chainfire has worked his magic again, releasing a new beta of SuperSU with support for the Galaxy Note7. There are a few caveats though, mostly due to new Samsung security measures inherent in the kernel, stopping Chainfire from using his usual exploits and instead having to apply workarounds.
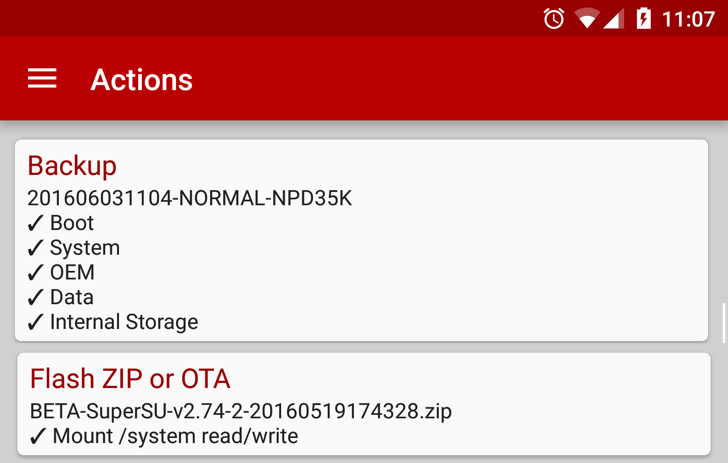
Chainfire's FlashFire is a very handy tool for anyone who likes to flash their phone. Provided the device is rooted, it enables the flashing of OTA files, ZIPs, and full firmware packages, all without needing a custom recovery. Previously, the app had been available in Google Play's beta program, but as of version 0.50, it is now open to all.

If you're into rooting these days, there's a good chance you've at least tried out FlashFire by well-known SuperSU developer Chainfire. It's one of the friendliest tools to use for flashing firmware images and mods, and it can even install official OTAs while keeping root intact. Today, Chainfire is releasing a new version of FlashFire with a pair of new features that will make it even more powerful: it can now create fastboot-flashable backups and there's a new option to preserve the existing recovery after installing OTAs and ZIPs.

We don't talk about rooting nearly as much these days. It's not that plenty of people aren't still doing it, but the popularity of modding has slowly dropped off as Android continues to mature. One of the leading deterrents to rooting is the hassle of manually staying current with updates, which can take more effort than it's worth–especially with Google adopting a monthly rollout schedule for Nexus security updates. Chainfire, developer of SuperSU, has updated his app FlashFire to take the pain out of keeping up-to-date by adding support for OTA packages and Android 6.0 Marshmallow.
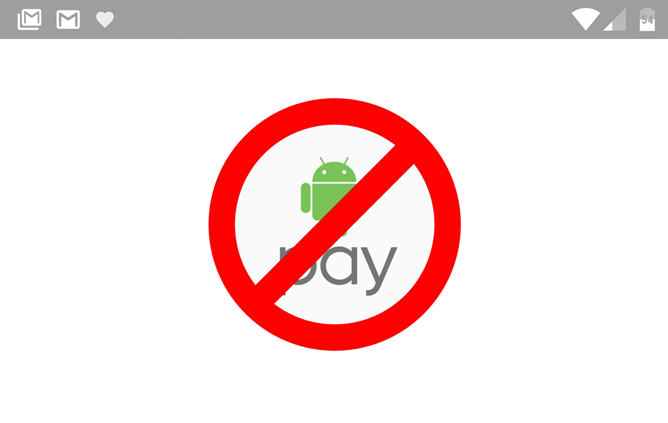
Well, it was nice while it lasted. A few months ago prolific Android developer Chainfire introduced a method of rooting Android devices without modifying the /System partition. It had the added and extremely welcome benefit of getting around SafetyNet detection for applications that were intentionally disabled on rooted phones, like Android Pay. But it looks like Google has caught on: starting this weekend (as reported on the /r/Android subreddit ), Android Pay and other SafetyNet apps no longer work with the roundabout root method. Bummer.

500px is the home of a great deal of lovely photography, and the app has been updated today to be a bit more lovely itself. At least this is the assertion made by 500px. The new v4.3.0 is live in the Play Store with a completely revamped UI and a few small feature additions. However, Chainfire's 500px wallpaper app 500 Firepaper got an update too, and it's a much sadder story.

If you've been modding your Android devices for any amount of time, you're probably familiar with Chainfire, developer of the extremely popular SuperSU root permissions manager and various other mods and apps. His latest work attempts to solve an annoyance that has bothered Android power users for years, but has become particularly annoying since the introduction of Android 5.0. Chainfire's new experimental method for rooting Android phones, tablets, and other gadgets does so without modifying any of the files on the /system portion of the device's storage, instead using a modified boot image.

Some people can't imagine using Android without root access. For those people, Nexus devices provide the surest way to maintain root without a bunch of monkeying around. Marshmallow has only started rolling out to devices, and already there's a new beta of SuperSU and modified boot images to root your Marshmallow devices.

Among the Android modding circles, there's no app more recognizable than SuperSU. It has a well-earned reputation as the de facto standard for rooting your phone, tablet, and really just about anything that runs Android. Chainfire, the creator and developer of SuperSU, has been maintaining it himself since 2012, but now he's ready to hand off the reins. In a post on Google+, Chainfire says he's transferring ownership of SuperSU to Coding Code Mobile Technology LLC, or CCMT.

Chainfire, the developer behind SuperSU as well as many other popular apps and mods, has published FlashFire, which he dubs the "spiritual successor" of Mobile ODIN. FlashFire is, as the name might suggest, a tool for flashing ROMs, kernels, and mods without the need for a custom recovery. It could (upon stable release) make these tasks, which generally involve a lot of button pressing and a little elbow grease, drastically simpler.









