
Cody Toombs
Senior Reviewer
Contributing since February, 2013
-
1511articles
-
1389News
-
12Features
-
1Lists
-
7Guides
-
37Reviews
-
65Deals
Page 6
About Cody Toombs
Cody has been writing with Android Police for ten years. While best known for the hundreds of APK Teardowns and breaking news on many of Google’s new products and services, he also covers deeper technical topics about the inner workings of Android, app development, and security. Cody is a software engineer and consultant with two decades of experience developing mobile and enterprise applications. In addition to writing, Cody is a regular podcaster and has made appearances on CNN, All About Android, and Tech News Today. Cody is also an active photographer and videographer, occasional gamer, and an all-around decent human.
What tech products or categories are you most passionate about?
Cameras and smartphones for photography. New technologies are bringing a lot of interesting things capabilities to the worlds of photography and video.
What was your first phone and what do you remember about it?
My true first phone was some old Motorola candybar phone from before the days of smartphones. I started on smartphones with the Cingular 2125 (a rebrand of the HTC Faraday, I think?)
Latest Articles
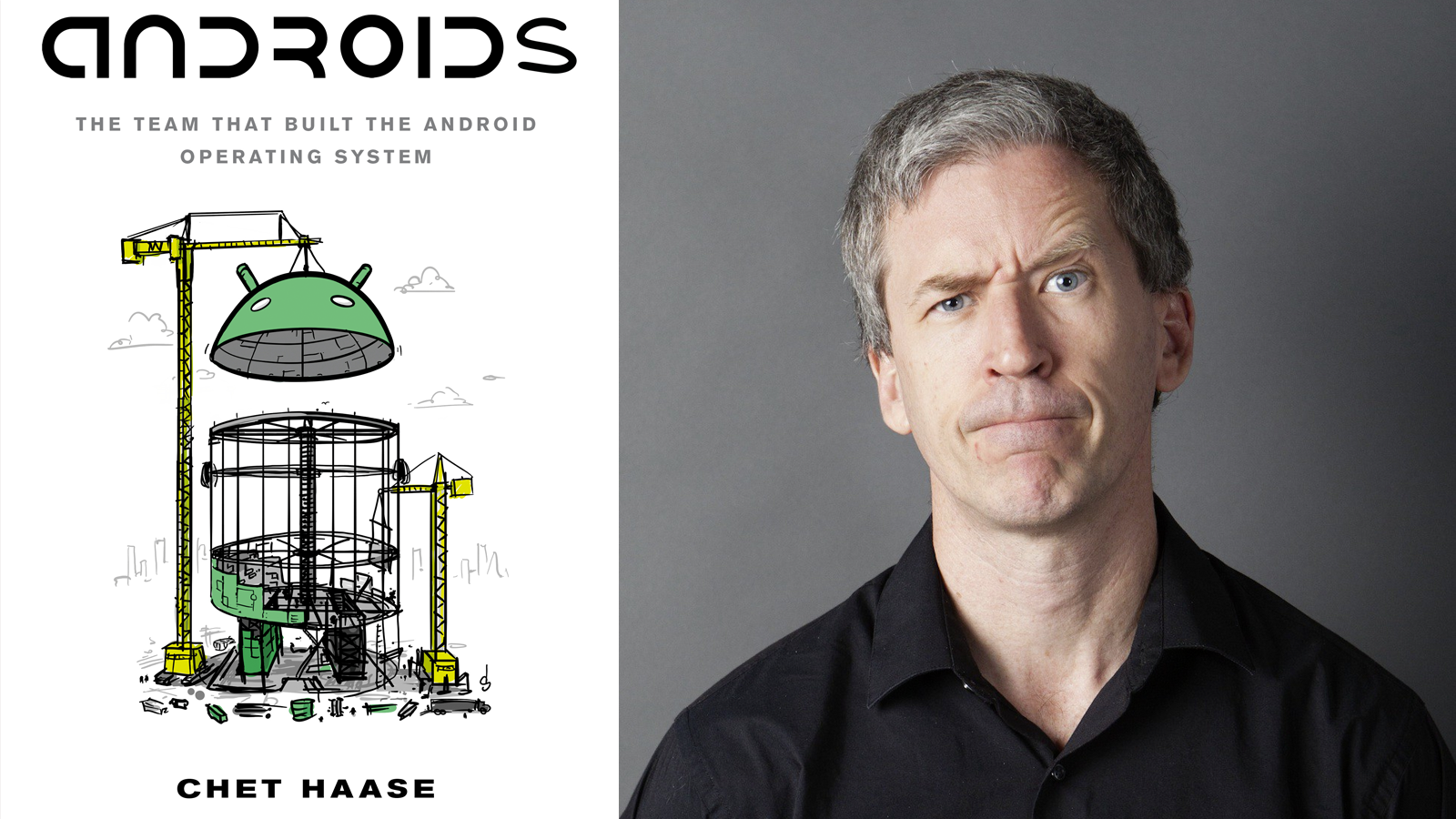
'Androids' by Chet Haase is on sale now, and you can get started reading for free
Available from both Google Play and Amazon Kindle

Read update
The history of Android has been told in many small parts; but to get the whole story you would have to scour thousands of blog posts, hundreds of podcasts, and the minds of a few dozen people that would probably ask you to leave them be — until now, that is. Androids: The Team That Built the Android Operating System is set to release tomorrow, bearing the tale of how the world's most widely used operating system came into existence. If you're curious about the backstory of the OS that you spend half your day staring at when you should really be working, you can buy the book now on Google Play and Amazon Kindle.Chet Haase, the author of Androids, is perhaps best known for delivering witty banter while hosting Google I/O fireside chats and developer sessions, or even educating people about bugs wherever they will let him. But he is also a longtime developer at Google with over a decade on the Android, working primarily on the UI Toolkit team; and he had a lot to do with enabling the smooth animations and visual effects of Material Design.[EMBED_TWITTER]https://twitter.com/chethaase/status/1424113349160144896[/EMBED_TWITTER]As Chet pointed out shortly after the original announcement last weekend, this book is meant for everybody, not just engineers. There won't be a lot of technical jargon, but instead it's filled with the events, experiences, decisions, and anecdotes of the people behind the green bot. And fear not, it has been confirmed on no uncertain terms, there will be puns.The ebook is now available for $9.99 USD from either Amazon or Google Play Books. If you would like to preview part of the book before purchase, samples are available from both stores. Amazon provides the first 4 chapters, while Google Play provides the first 7 chapters (about 20% of the total book).

Android Auto starts suggesting music, news, and podcasts, so you can keep your focus on the road
Google is probably also trying to subtly fix your listening habits

We've heard it all along, Android Auto is designed around keeping your hands on the wheel and your eyes on the road. While that doesn't always work out in practice, many of the changes to the Auto interface are at least intended to streamline your interactions with the screen. It looks like Google may have identified people were spending too much time browsing for music and podcasts, because a new shortcut now provides automatic suggestions that can get you listening without a lot of tapping.

Smart Displays and the Assistant are getting new tools to keep your home organized, entertained, and educated
Family Bells ring on devices, plus checklists, routine triggers, new stories, and educational tools

While our daily routines probably aren't as routine as they once were, Google is preparing another round of improvements to Assistant that will make it easier to take control of your activities. Several of the new features are aimed at scheduling and keeping organized, but there are also some great additions to storytelling content and new educational tools coming soon.
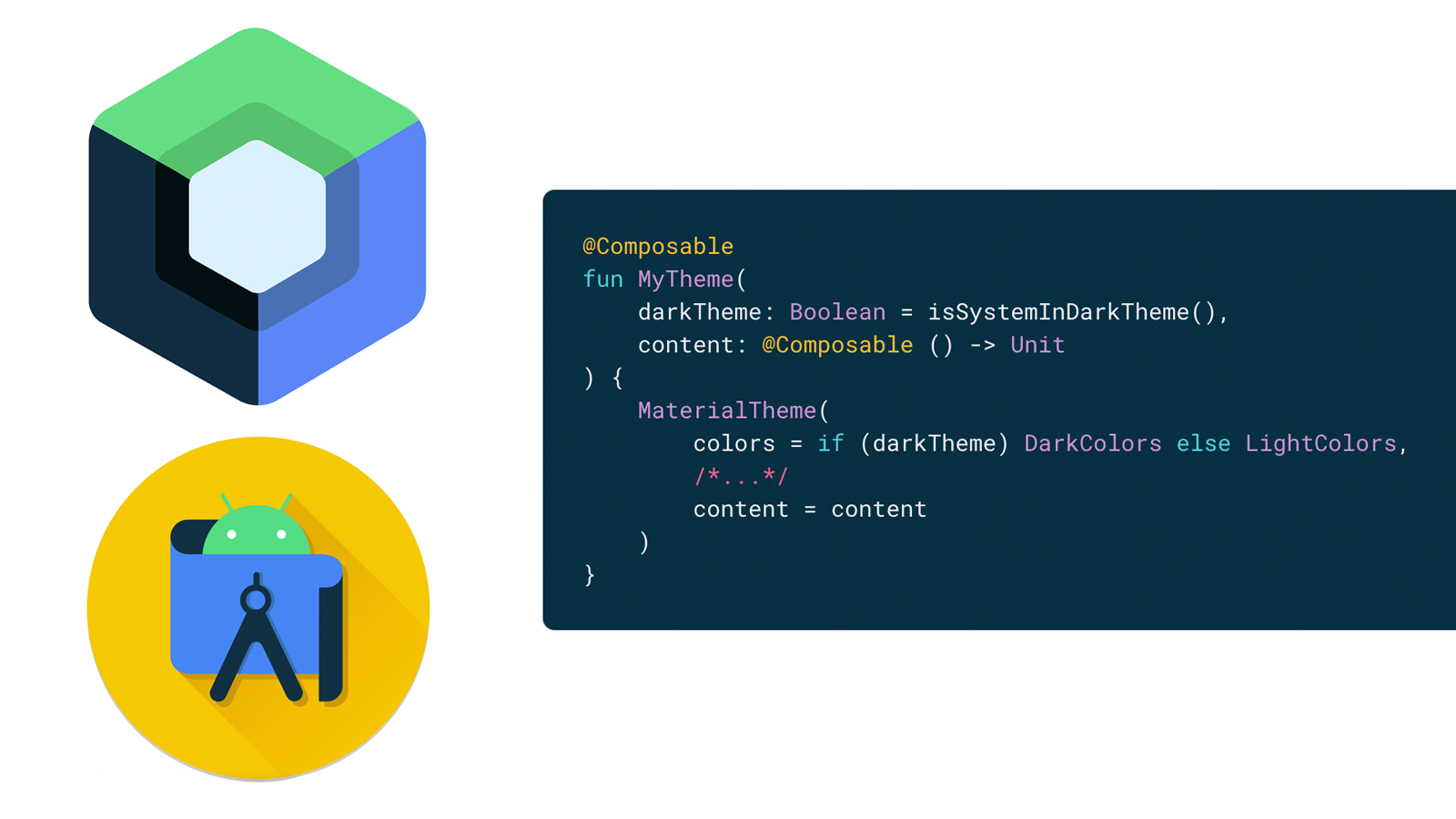
Google's UI tool Jetpack Compose reaches stable build after two years of development
Android development is better than ever

Since its introduction during I/O 2019, Jetpack Compose was obviously destined to become the prescribed method of Android UI development. After more than two years in public development, it has hit the milestone many developers have been waiting for: an official 1.0 release. Alongside a stable release of Android Studio Arctic Fox, Jetpack Compose is ready for use in production code.

Moment launches Galaxy S21 cases with MagSafe support
Available for $35 during the current sale

Apple's iPhone 12 made waves with the addition of MagSafe, kicking off the beginning of a whole new ecosystem of accessories. While the charging capabilities are proprietary to Apple's own product line, there's still quite a bit that can be done with the magnetic mounting system. If you happen to be walking around with a Samsung Galaxy S21 while also eyeing one of the new MagSafe mounts for your car or desk (or a tripod), Moment has a case that will bring the two together — and it happens to be on sale for the next week.
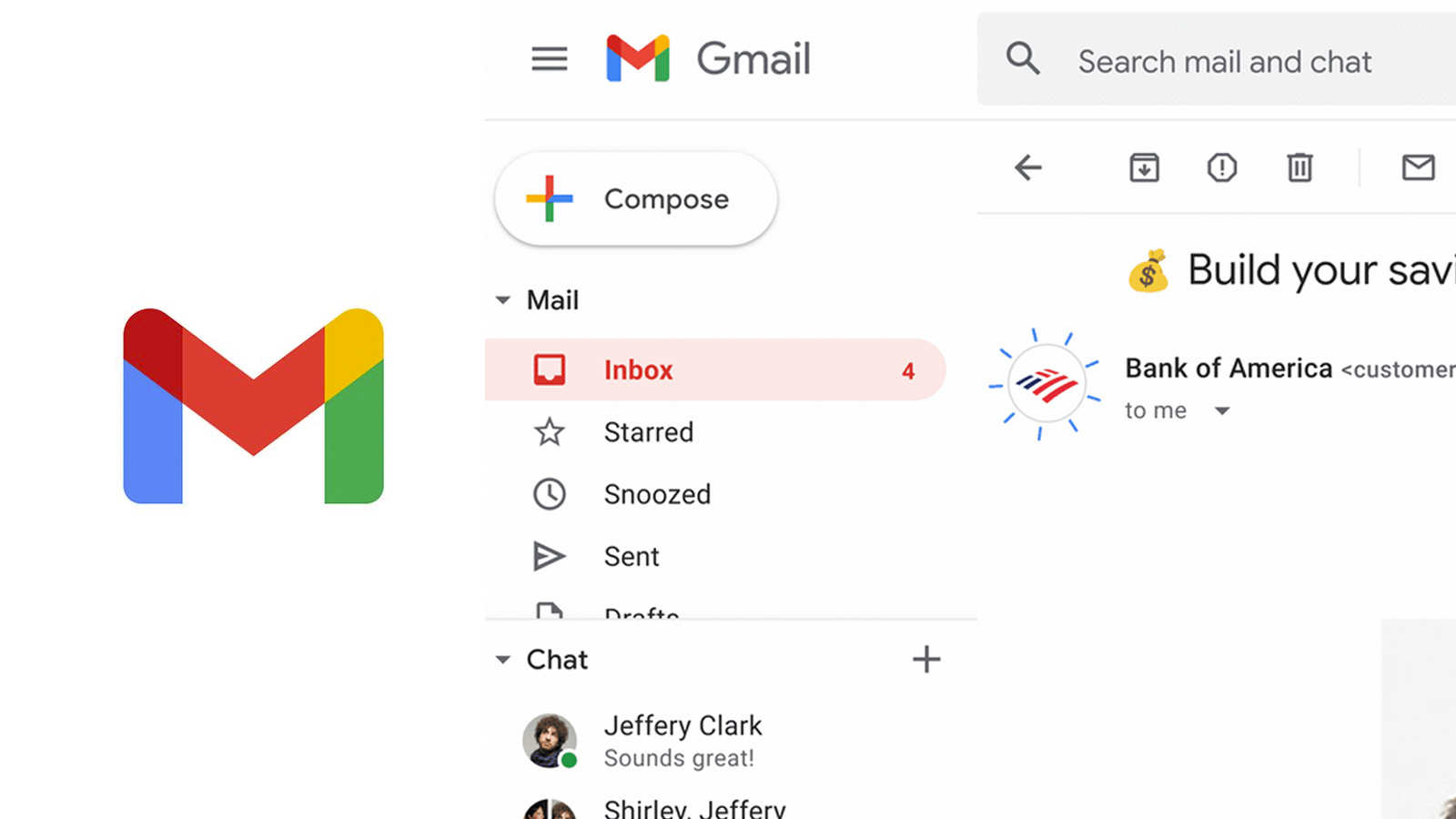
Gmail's latest anti-fraud measure promises to show you corporate logos
Logos in place of the avatar show an email has gone through rigorous verification

Despite years upon years of attempts to drown out phishing scams from the email ecosystem, fraudulent messages are still painfully commonplace. Last year, Google announced support for BIMI, a standard aimed at verifying major organizations and loading in additional metadata for improved security. The rollout began with G Suite users almost a full year ago while the bugs were worked out of the system, but it's now coming to the rest of Gmail.

Review: Forget the Chromecast, Walmart's Onn Android TV is cheaper and just as good
It's practically the same thing, but almost half the price

While smartphones regularly threaten to get more expensive every year, somehow the market for set-top boxes and HDMI dongles is dropping to seemingly impossible lows. When we were introduced to the Chromecast with Google TV last year, with 4K HDR support and the full capabilities of Android TV, it felt like a $50 gadget would be the best we could ask for. As it turns out, a new contender with similar specs and an even lower price has come from an unlikely source: Walmart... And it's pretty damn good.

Google has a new app to help you fly your drone safely in the US
Well, new to America

It can feel a little overwhelming to begin flying drones when you're just getting started. Not only do you have to get registered and learn how to actually operate a drone, but you need to learn where you can legally fly. Fortunately, as the tired saying goes, there's an app for that — quite a few, in fact. Wing, a subsidiary of Alphabet (Google's parent company), actually built one such app called OpenSky, but it has been effectively limited to Australia since it launched. However, the app is lifting off from the land down under and making a landing in the US.

This smartphone gimbal will take your TikToks and Instagram videos to the next level
Review: Zhiyun Smooth-Q3 — Designed for creators

Smartphone gimbals have progressed quite a bit over the years, first serving just as tools to keep the image steady, but eventually evolving more targeted features and designs. Zhiyun released the Smooth-Q2 in 2019, and its small size and sturdy design made it ideal for travel. Now the brand new Smooth-Q3 is out, but this time the design and features are directed toward vloggers and social networking.

Google really wants developers to adopt its new Material UI
Google isn't making devs wait to start working on the new stuff

Android development may have started as a grab bag of poorly integrated libraries with no documentation and running it all in a bad IDE, but things have really turned around over the years. Android Studio makes it easier to build working apps with fewer mistakes; Kotlin makes for more readable straightforward code; and the combination of Jetpack and Jetpack Compose provides a clear direction for faster development. Today's announcement really focuses on Jetpack Compose, but as you would expect from each Google I/O, new versions of each are coming out and they've got something new for everybody.

Flutter 2.2 announced for faster, less crash-y apps
Pushing harder on sound null safety

Flutter's popularity has been exploding recently, and it's not hard to see why. The cross-platform framework made huge strides with the release of v2.0 a couple months ago when it gained official support for every major OS available, received substantial tooling enhancements, and made inroads toward protecting against instability with the addition of sound null safety. Now Google is taking an opportunity at I/O 2021 to announce Flutter 2.2.
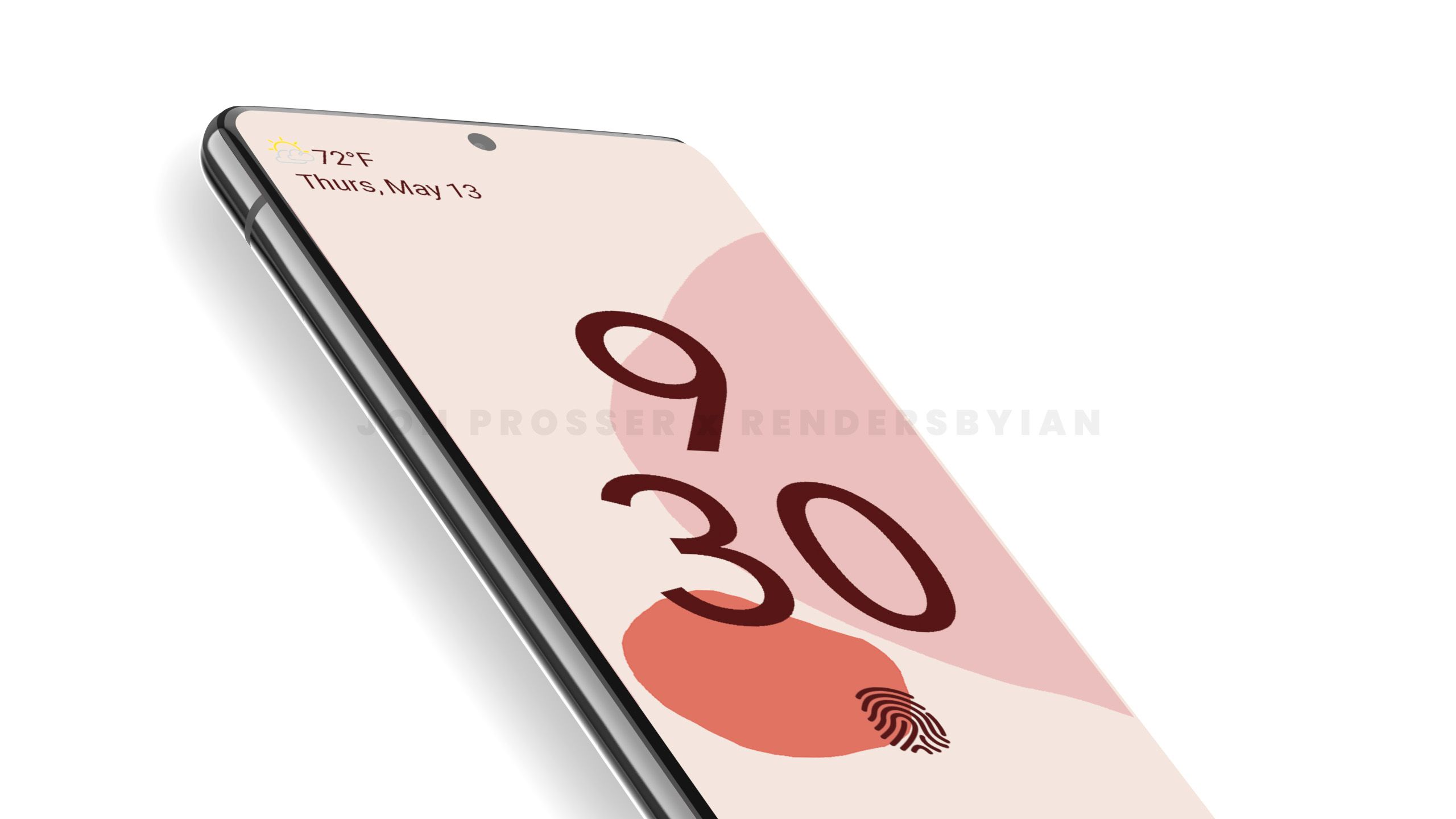
Google Pixel 6 and Pixel 6 Pro leak reveals a totally new look and hardware
A new look and camera could bring renewed energy to the Pixel line

It's virtually impossible to bring a notable tech product to market without it getting leaked at least a little, and Google's smartphones are almost famous for the extent to which they're leaked ahead of release. Now it looks like the Pixel 6 may be facing the same fate as a new leak reveals a new camera and a fairly substantial departure from the simple, subdued design language we've come to expect from Google's hardware group.

One Apple exec actually wanted to bring iMessage to Android back in 2013
Apple already admitted that iMessage for Android was killed to keep its walled garden

The legal conflict between Epic Games and Apple has already had some fairly substantial fallout. The court of public opinion pressed Apple and Google to reduce marketplace fees for developers on the App Store and Play Store, and a number of Apple's antics have fallen under the scrutiny of politicians and the general public. The hearing also shined light on iMessage's Apple exclusivity, with the company admitting that it kept the messaging platform from Android in order to create a lock-in effect. But apparently that stance wasn't shared with everyone across the board. It turns out that Apple executive Eddy Cue wanted to bring iMessage to Android in 2013, only to be shut down by peers, as a new deposition shows.

Android 12 DP3 relocates the stacked notification count
Sometimes it's the little things that help the most

Just about every major Android update has come with some changes to the notifications, sometimes in the form of major functional additions, or possibly just some minor layout tweaks. Google already made a change in the first Android 12 developer preview to put notification snoozing in a more easily accessed location, but the latest update to DP3 is adjusting the layout of stacked notifications so the total is more visible and makes better use of space.
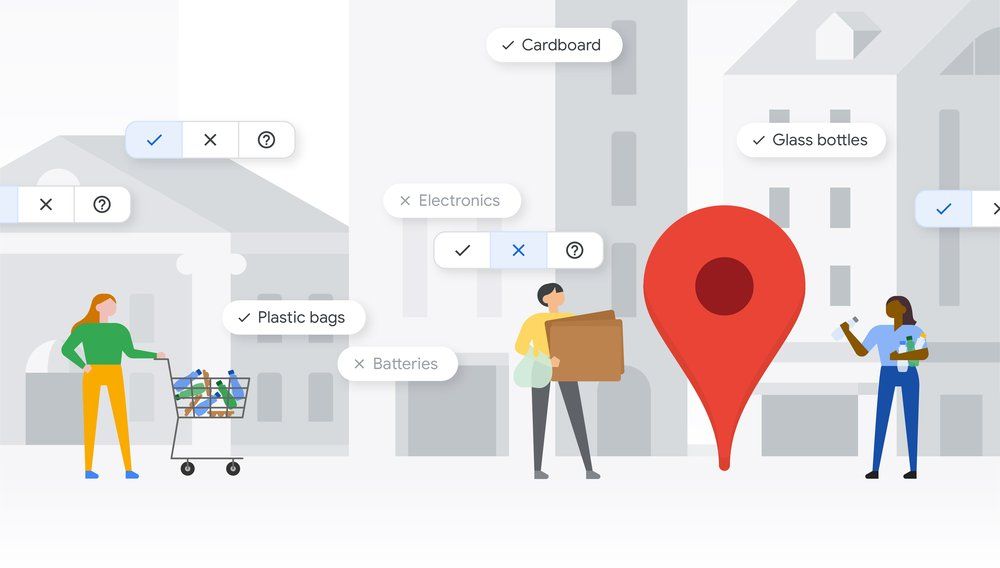
Google Maps is helping people find places to recycle their junk
Making it just a little easier to keep the planet clean

Tech companies frequently talk about new initiatives to reduce their impact on the environment, but it's unusually uncommon that those projects have help other people take part in doing the same. Google Maps is jumping in with a new set of tools that make it easier for people to find out where they can dispose of their used up materials so they can be recycled properly.
Google Pay just gave you an extra 11 days to earn your free $30
So don't leave it to the last minute this time

Read update
When billion dollar corporations offer to pay you for something you're already doing, take that opportunity while it's there. Starting April 12, Google Pay is launching the Spring Challenge, a 10-day contest to perform tasks that will potentially earn a gift of $30. It's not quite as easy or straightforward as dropping by the store every day to buy packs of gum, but it should be easy enough, and you can even help your friends.
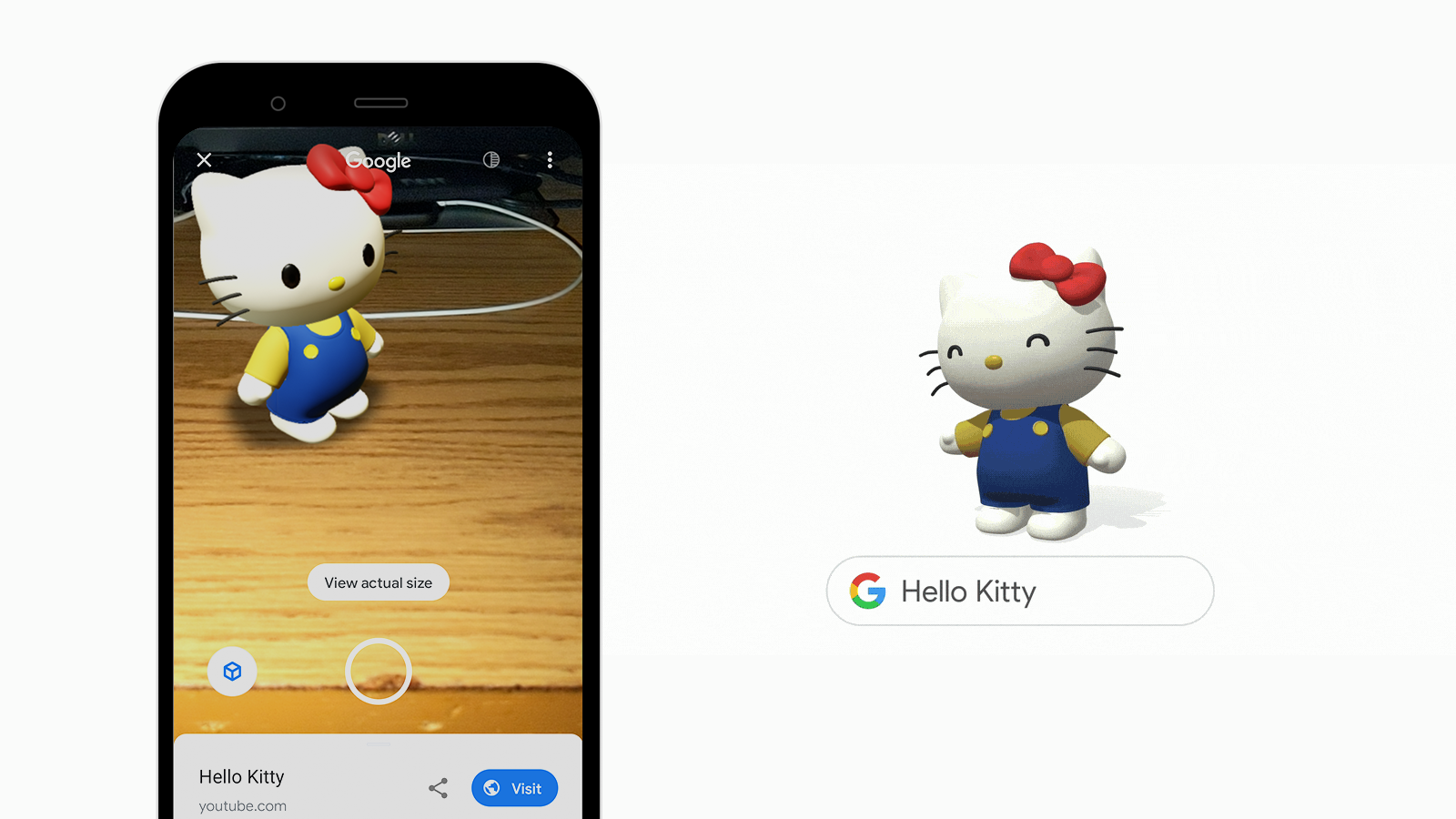
Play with an AR Gundam mech on your smartphone
Watching PAC-MAN go in a circle is a little mesmerizing

Google loves to demonstrate its ability to create fun toys, particularly with the use of augmented reality. We've seen plenty of AR demonstrations in the past with animals and other common objects, and there have even been some trademark collaborations to play with, but now Google is diving into the world of anime with an assortment of iconic Japanese characters like PAC-MAN and Gundam.

DJI's new ultraportable drone is a sleeper camera powerhouse
All the best things from DJIs previous drones packed into one

If you've been thinking about getting a drone for those beautiful aerial photos and videos, DJI just gave you a new option to consider. As a follow-up to last year's Mavic Air 2, DJI is now launching the Air 2S — sans Mavic branding. The name and body might look nearly identical, but this isn't just a small revision; DJI is packing its latest model with a big new camera sensor and some other powerful new features.

Read update
What's more cost-conscious than buying a budget phone? Buying a budget phone while it's on a really good sale. Samsung's Galaxy A21 isn't going to blow away anybody with camera quality or performance, but it's a good phone that came out at an already affordable $250. However, if you're looking to replace an old or broken phone, you can snap up the A21 from Amazon for just $149.

Grab a Samsung Galaxy Tab S7 (Wi-Fi) for its lowest price ever
On sale for 18%-25% off

It was only a three weeks ago that the Samsung Galaxy Tab S7 hit a record low of $630, and at that time it was a fairly good discount on the original selling price of $700 for the base model. If you were on the fence then, the latest sale may be tempting enough to seal the deal. The Wi-Fi model is currently running for between 18% - 24% off, depending on storage size and accessories.
